HOW TO PREVENT ATTACK BY HACKER AT COFFEE SHOP – TECHNICAL ARP SPOOFING
With the immense effects of IP spoofing attack , each of us needs to be aware of how to prevent IP spoofing. Here are a few steps you can take to protect devices, data, networks, and connections from IP spoofing.
For personal
To avoid hackers using Phishing attack to cheat on the Internet, collect your personal data, sensitive information. Please note the following points:
- Beware of emails that tend to urge you to enter sensitive information. No matter how appealing the call-to-action is, it’s still worth checking it out. For example: you just shop online, suddenly there is an email from the bank to offer you a refund, just enter the card information used to pay. Believe it ?!
- Do not click on any links sent via email if you are not 100% sure it is safe, as spoofing technology does this.
- Never send confidential information via email.
- Do not reply to scam emails. Fraudsters often send you phone numbers for you to call them for business purposes. They use Voice over Internet Protocol technology. With this technology, their calls can never be traced.
- Use Firewall and anti-virus software. Remember to always update to the latest versions of these software.
- Limit the use of public , unsecured WiFi. If you must use public networks such as in cafes, airports, etc., use a VPN. This is a tool to help encrypt internet connections, to protect private data in the process of sending and receiving data on the internet if you don’t want to be attacked by hackers using spoofing.
- Use secure software solutions like VPN . In addition, anti-virus software also helps to scan incoming traffic for malware. However, the most important thing is to update these software regularly to ensure you always have the latest patches and security and authentication technologies.
- Use secure encryption protocols to secure traffic to and from the server. In it, always make sure ” HTTPS ” and the padlock icon are always in the URL bar of the websites we visit.
- Please forward spam messages to [email protected]. You can also email [email protected] This organization helps fight other phishing .
For organizations and businesses
- Training for employees to increase their knowledge of safe internet use. Regularly organize training sessions, rehearse situations for spoofing techniques
- Using the G-suite service for business, it is not recommended to use the free Gmail service because it is easy to spoof.
- Implement SPAM filter to prevent spam and phishing
- Always update software and applications to avoid security holes that can be exploited by attackers.
- Proactively secure sensitive and important information. See more Information security solutions for businesses.
Useful tools to help prevent Phishing:
- SpoofGuard : is a browser plugin compatible with Microsoft Internet Explorer. SpoofGuard places an “alert” in the browser toolbar. It will turn from green to red if you accidentally go to a phishing site. If you try to enter sensitive information into a form from a fake site, Spoofing will save your data and warn you.
- Anti-phishing Domain Advisor : essentially a toolbar (toolbar) to help warn of phishing websites, based on data from Panda Security company.
- Netcraft Anti-phishing Extension : Netcraft is a reputable unit that provides security services that include many services. Among them, Netcraft’s anti-Phishing extension is highly appreciated with many smart warning features.
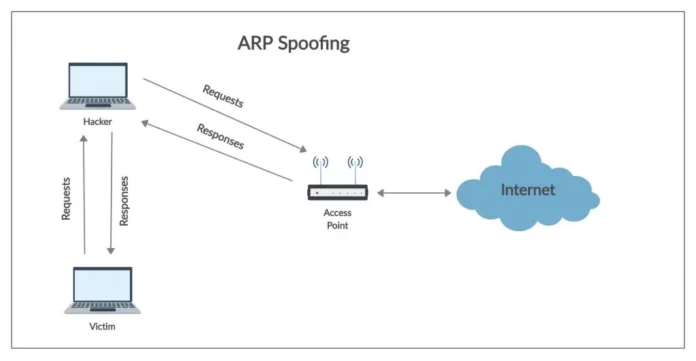
Use the command :
- ipconfig /all see my MAC
- arp -a see the ARP table on your computer, check if B’s MAC is the correct MAC B or not.
- arp -d * deletes the entire ARP table on your computer, so the hacked MAC addresses are also lost, and the computer will start learning again. But if the attacker continues to pump poisoned ARP packets, deleting this ARP table is also useless
- arp -s permanently attaches the destination IP to its real MAC, so the attacker can’t poison this IP anymore. But this is not feasible for large networks, many computers, and with IP changes (eg using DHCP).
Using software:
- We can install Anti ARP software to avoid receiving ARP Reply spoofing
Use device :
Dynamic ARP Inspection: The switch will rely on the DHCP Snooping Binding table to check the sent ARP Reply packet is valid or not, if not, it will DROP immediately.
SWITCH(config)#ip arp inspection Vlan
SWITCH(config)#ip arp inspection validate ?
Reference : http://www.cisco.com/en/US/docs/swit…de/dynarp.html